Avoiding Tech Neck
The strain on people’s bodies isn’t always taken seriously when someone works at a computer. Still, many official studies suggest that desk jobs can have a radical and rather negative effect on the health of individuals. One common ailment is what is called “tech neck.” Tech neck is a term that describes neck pain and damage stemming from looking down at computers or mobile devices for prolonged periods. To avoid tech neck, you can follow these helpful tips.
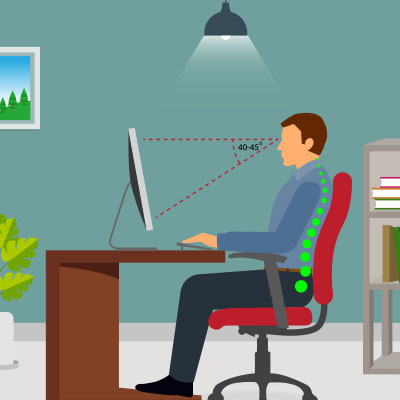
Adjust Your Screen’s Height
If sitting and working at a computer is a giant pain in the neck, you will first want to ensure that your computer monitor, laptop, or mobile device is positioned at eye level. To accomplish this, you can utilize a stand or elevate your device so you don’t have to look down for extended periods. Maintaining a more neutral neck position can reduce strain on the neck muscles.
Take Regular Breaks and Stretch
People are busy. That is no joke. If you schedule breaks during your screen time to allow your neck muscles to relax and incorporate simple neck stretches and exercises into your breaks, it can take a lot of pressure off your neck. One tip is to rotate your neck gently, tilt it from side to side, and perform shoulder rolls to relieve tension.
Practice Proper Posture
Be mindful of your posture when using devices, as this can have the most significant effect on whether or not your neck will ache. You will want to sit straight with your shoulders relaxed, and your spine aligned and avoid hunching over or craning your neck forward. Instead, you should always keep your head in a neutral position.
Working at a computer shouldn’t be a pain in the neck. You can significantly reduce the risk of developing tech neck by consistently practicing good posture, taking breaks, and making ergonomic adjustments to your workspace.
At White Mountain IT Services, we want you to use technology to your benefit, and that can’t happen when your health deteriorates from tech neck. If you would like to see more technology-related articles, please return to our blog again soon.

