
Comprehensive Cybersecurity Assessment in New Hampshire
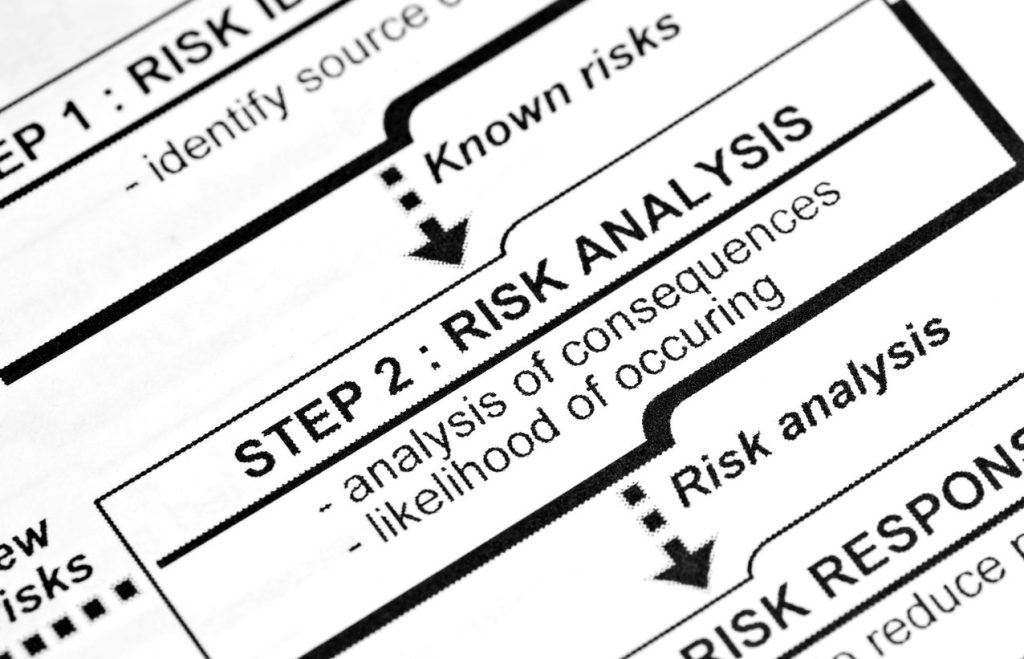
White Mountain IT can conduct a comprehensive IT risk assessment to help identify, analyze, and evaluate the potential risks to your organization’s IT systems and infrastructure. The purpose of an IT risk assessment is to identify vulnerabilities and threats that could compromise the confidentiality, integrity, or availability of an organization’s IT assets and to prioritize the risks based on the potential impact to the organization.
White Mountain can perform a variety of IT risk assessments,
we follow a structured process to help make it as simple as possible.
Examples of IT Assessments that we can help with:
-
- Vendor Security Assessment – Evaluate the security posture of your third-party vendors to mitigate risks from external partnerships.
- Cloud Maturity Assessment –Assess the readiness and effectiveness of your cloud strategies and identify areas for optimization.
- IT knowledge Transfer Risk Assessment – Ensure smooth transitions in IT roles and safeguard critical knowledge during team changes.
- IT Policy, Standards and Procedure Assessment – Analyze existing IT policies to ensure alignment with industry standards and best practices.
- IT Service Desk Maturity Assessment – Improve service desk efficiency by evaluating current capabilities and identifying opportunities for growth.
- Current State of IT Assessment – Gain a clear understanding of your organization’s overall IT environment and performance.
- IT Skills Assessment – Evaluate the technical proficiency of your IT team to identify skill gaps and training needs.
- Internal Controls Self Assessment – Strengthen governance by reviewing internal controls and ensuring compliance.
- Office 365 Capability Assessment – Maximize the productivity of your Office 365 suite by analyzing its implementation and usage.
- Service Management Maturity Assessment – Enhance service delivery by identifying the maturity level of your IT service management processes.
- IT Team Effectiveness Assessment – Measure the effectiveness and collaboration of your IT team to boost overall performance.
- Threat and Risk Assessment – Identify and prioritize potential threats to your IT infrastructure to mitigate risks proactively.
- Cyber Security Insurance Assessment – Review your cybersecurity insurance coverage to ensure adequate protection against evolving threats.
Regularly reviewing and updating IT risk assessments is crucial for maintaining a secure and robust IT environment. With White Mountain IT Services Cybersecurity Solutions, you can trust that your organization is well-equipped to navigate challenges and fortify its defenses in a dynamic technology landscape.
Cybersecurity Frameworks and Standards for IT Risk Assessment for your Nashua Business
There are several cyber security frameworks that organizations can use to help them manage and mitigate cyber risks. These frameworks provide guidance on best practices for protecting an organization’s information and systems from cyber threats. Although some frameworks are specialized, both NIST CSF and CIS Implementation Group 1 are solid first steps, and provide basic cyber hygiene guidelines for any organization. Some common cyber security frameworks include:
- NIST Cybersecurity Framework (CSF): Developed by the National Institute of Standards and Technology (NIST), the CSF is a risk-based framework that helps organizations identify, protect, detect, respond to, and recover from cyber threats. It provides a common language and set of standards for managing cyber risk and aligns with other security frameworks, such as ISO 27001.
- CIS Controls: The Center for Internet Security (CIS) has developed a set of 18 critical security controls that organizations can use to defend against common cyber threats. The controls are organized into three categories: foundational, organizational, and technical.
- NIST SP 800-171 has gained popularity due to requirements set by the U.S. Department of Defense regarding contractor compliance with security frameworks. Government contractors are a frequent target for cyber attacks due to their proximity to federal information systems. Government manufacturers and subcontractors must have an IT security framework to bid on federal and state business opportunities.
- Cybersecurity Maturity Model Certification (CMMC): Developed by the U.S. Department of Defense (DoD), the CMMC is a framework that assesses an organization’s cyber security posture and provides certification at various levels of maturity. It is intended to help ensure that DoD contractors and their subcontractors have sufficient cyber security controls in place to protect sensitive information.
No single framework is a one-size-fits-all solution, and you may need to use a combination of frameworks to meet your specific needs and requirements. It’s important to regularly review and update your cyber security framework to ensure that it remains effective and aligns with the organization’s current risk profile.
Comprehensive Cybersecurity Services in Nashua | White Mountain IT Services
At White Mountain IT Services, we provide thorough IT Risk Assessment in Nashua to safeguard your organization’s IT infrastructure. Our process is designed to identify, analyze, and evaluate potential risks that could threaten the security, functionality, and availability of your IT systems. By conducting a detailed risk assessment, we help businesses uncover vulnerabilities, mitigate threats, and ensure the resilience of their technology assets.
Our assessments focus on key areas such as system vulnerabilities, external threats, and internal processes that may compromise the confidentiality, integrity, or availability of your IT resources. By prioritizing risks based on their potential impact, we enable your organization to make informed decisions about security enhancements and resource allocation. Trust White Mountain IT Services to help you strengthen your defenses and protect your critical business operations.
Cyber Compliance Services
Cybersecurity and compliance can be incredibly frustrating, especially for small to mid-size organizations that may not have qualified staff to dedicate to the process.
Compliance requirements can be a complicated maze of regulations and requirements, are being forced onto more industries, and smaller organizations every day.
That is where White Mountain IT comes in. We meet you where you are and help you set a course that makes security and business sense.
Whether your interest in cyber compliance is being forced by industry, government, client requirements, insurance, or simply adherence to corporate governance and best practices, we can help.

Featured Services
To Pay or Not to Pay? Why Giving In to Ransomware is a Losing Game
A ransomware attack can feel like a hostage situation. Your data is encrypted, your operations are at a standstill, and a countdown timer is ticking away alongside a demand for thousands—or even millions—of dollars in cryptocurrency.
4 Steps to Prepare Your Business for AI
Artificial intelligence is becoming the secret sauce for competitive small businesses. Unfortunately, there is a massive catch: You can’t simply plug in AI and expect magic to happen. It takes a strategy. To help you prepare, here is a roadmap to ensure your business is AI-ready.
The Longer the Better! Why to Ditch Your Short, Complex Passwords
You’ve probably heard a lot of password advice over the past decade, but how much of it is actually good advice that you should listen to? These days, with advanced automated threats able to crack incredibly complex passwords with ease, you can’t be too careful. You might even need to take a different approach entirely… which brings us to the OG password advice: just make it longer.
3 Ways to Turn Your Tech Stack Into a Growth Engine
For years, the firewall was seen purely as a defensive tool—an all-in-one solution with antivirus, web filtering, and intrusion protection. Nowadays, they can potentially serve a much greater purpose beyond simple network security. When leveraged right, you can use the immense amount of data firewalls track to identify bottlenecks, optimize workflows, and make smarter infrastructure investments.
Connect with White Mountain IT Services for Your IT Risk Assessment in Nashua
Protecting your business against evolving IT risks requires proactive and comprehensive strategies. At White Mountain IT Services, we specialize in Cybersecurity Services in Nashua, providing tailored solutions to identify vulnerabilities, strengthen your security posture, and align your systems with industry standards.
Our team is committed to safeguarding your organization’s data and ensuring compliance with the latest cybersecurity frameworks. Whether you need a one-time assessment or ongoing support, we have the expertise to keep your operations secure and resilient.
Take the first step toward a safer, more reliable IT environment. Contact White Mountain IT Services today to learn how we can help your business mitigate risks and achieve peace of mind. Let’s build a secure future together!

