Tip of the Week: How to Add User Profile Management to Google Chrome
Why have you never seen this function before? It?s simple, really – the mad scientists at Google probably felt like their experimental add-ons weren?t ready for the world to use yet, and they demand use from only the best, brightest, and bravest individuals. By this, we are referring to the disclaimer at the top of the web page, chrome://flags:
While your computer might not spontaneously combust, these add-ons do warn the users that they may come with certain unwanted functions, such as deleting browser history, private information, security information, and randomly disappearing at any given time. This means that you should always be using the most up-to-date version of Chrome, as well as using a quality antivirus software and firewall solution.
Here are the steps you must take to lock your Google Chrome browser window:
Step 1: Finding the Right Add-On
In order to locate the list, visit the chrome://flags web page that we mentioned above. This will bring up a list of all experimental features that are associated with Google Chrome. You are looking for Enable new profile management system:
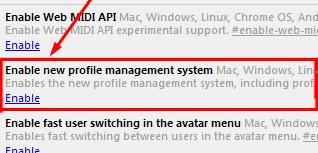
It?s a fair ways down the page, so to save yourself a lot of time and reading, simply use the CTRL+F (find) function to locate the correct feature.
Step 2: Enabling the Add-On
Once the not-so-hard part of finding the appropriate add-on is over with, all you need to do is click on Enable. Then, all you need to do is re-launch Google Chrome and the extension will be active.
You?ll notice that the sign-in screen looks similar to those used by Microsoft Windows operating systems. You select a user and enter in your Google account password, and you?re all set to browse the Internet. This helps protect your web browser from those who would use it to look at peculiar? things, without your permission.
Kinks in the System
As with most software add-ons, there are some undesirable features that come with this basic user login system. For those who have two Google accounts associated with their system user profile, you will not be able to logout of your primary account to use Google Drive with another one. This makes it difficult to move between two accounts at will, and can be infuriating for those who must use more than one account. Furthermore, the primary Google account for the browser would save open windows and tabs, but the secondary accounts would not, instead opening up to Google?s home page.
Of course, if you don?t like the way that something is working, you can always remove it by visiting chrome://flags and clicking Disable, then relaunching Google Chrome.
This add-on is a good security measure for your browser, but keep in mind that, while using a Chrome add-on is a good idea to keep unwanted users off of your computer, you will still want to have an enterprise-level network security solution in place to safeguard against malware and hackers.

